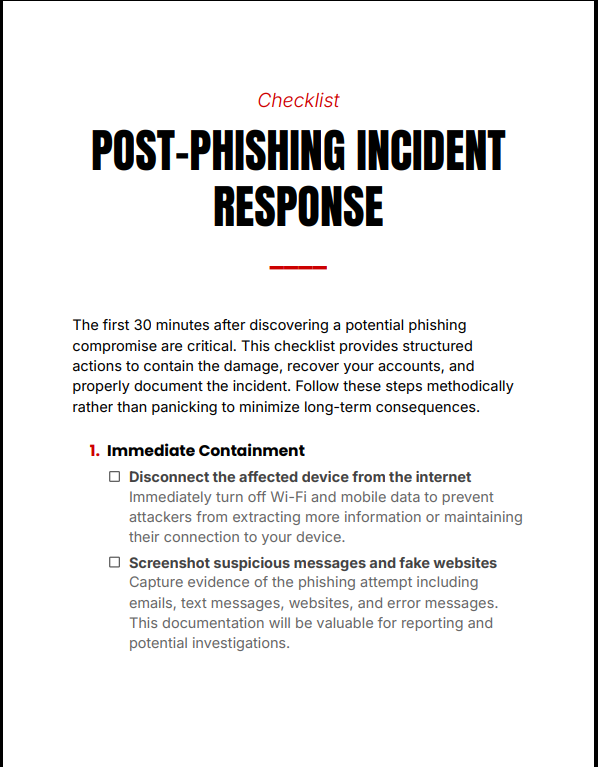
Checklist Overview
Post-Phishing Incident Response Checklist provides a structured, no-panic response system for handling phishing incidents. Instead of reacting emotionally, this checklist guides you through precise, time-sensitive actions to contain threats, secure accounts, and document the breach effectively. Designed for clarity and speed, it ensures you don’t miss critical steps when every minute matters.
What You Get
- Printable checklist (PDF)
Contents
- 1. Immediate threat identification and confirmation
- 2. First 30-minute containment actions
- 3. Password resets and account lockdown procedures
- 4. Email, banking, and social account recovery steps
- 5. Device security checks and malware scans
- 6. Incident documentation and reporting guidelines
- 7. Post-incident prevention measures
Why This Checklist Matters
During a phishing attack, hesitation and confusion increase damage. Post-Phishing Incident Response Checklist eliminates guesswork by providing a clear execution path—helping you act quickly, reduce exposure, and regain control before the situation escalates.
Features
- Time-critical action flow for immediate response
- Simple, structured checklist format for zero confusion
- Covers full response cycle from detection to prevention
Who This Is For
- Anyone who suspects or confirms a phishing attack
- Students and professionals handling sensitive accounts
- Individuals who want a ready-to-use cyber incident response plan
Format & Delivery
Instant PDF download after purchase. The checklist link is sent to your email and can also be accessed in My Books page.
Sample
Preview a section of the checklist above.
Customer Guarantee
FAQs
- How will I receive the checklist? Instant PDF link after purchase; check spam if you don’t see the email. Also available in My Books page.
- What format is included? PDF (printable and digital use).
- Refund policy? 7-day refund policy—see refund terms below and contact support with your order number.
Price
$3 — Full Access